As the premier, Indianapolis IT Consulting company, we help area businesses feel confident in their technology by providing the services to allow them to gain control of IT support and IT service issues. We are proud to be Indiana-based serving: Indianapolis, Fishers, Carmel, Greenwood, and Muncie.
We know the frustrations of IT. That's why we provide a wide list of services designed to meet your unique IT needs.
We provide and variety of services
What services are best for you and your business?
Every company is unique and, therefore, requires its own unique IT support and solutions. That is why, at Leap Managed IT, our services begin with an IT Master Plan!
With an IT Master Plan, you can uncover technology obstacles, develop a tailored IT blueprint, learn what questions to ask, and grow your business.

Ridiculously Helpful IT Support



Check out what our customers are saying about us
“I really appreciate LEAP’s willingness to come in and learn what we know, and understand what we don’t know. I never feel like they are trying to oversell us. And they’ve never made a promise that they couldn’t keep. ”
“The level of expertise and knowledge LEAP Managed IT provides us is a game changer. Our business is fast paced, growing and highly mobile so we have to use technology to stay lean and deliver a great customer experience. LEAP’s IT support team helped us move to our new corporate offices and handled every aspect of technology. They were integral in making the transition easy and pain-free. Having a partner to worry about the technology is a big deal. We couldn’t do this on our own. ”

Starting new IT consulting and HIPAA compliance project in Fishers today
Repaired an ADF unit for Midwest Center for Joint Replacement.
Repaired a doc feeder for Midwest Center for Joint Replacement.

Working in downtown Indianapolis to assist a client with IT Support.

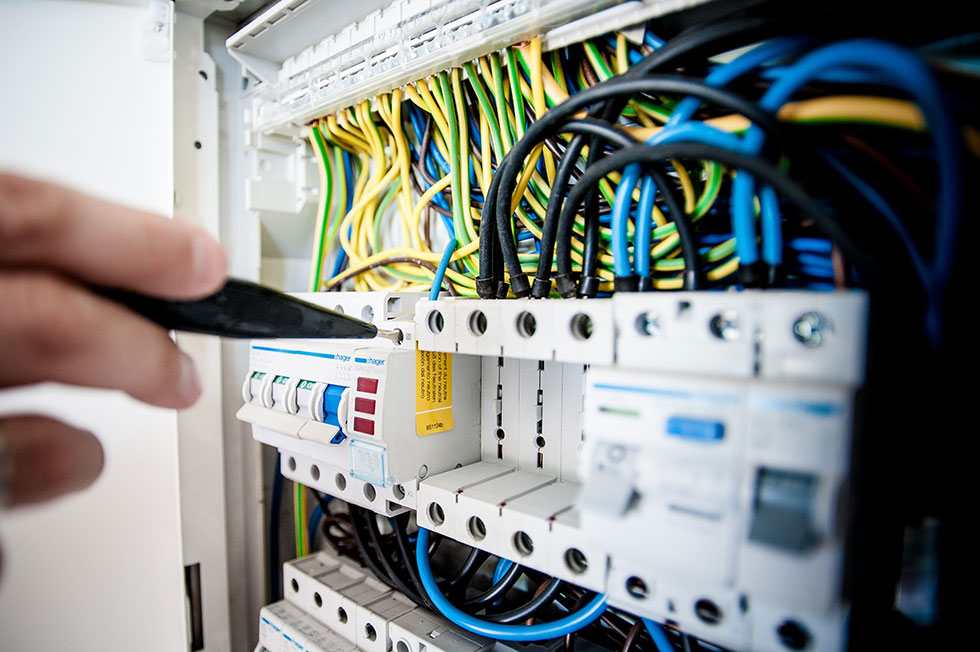
Planning out a new facility IT project in Zionsville Carmel area. Structured cabling, network switch deployment and new PC installs are all in the works

IT consulting visit with manufacturing client in Columbus, Indiana. Planning out transition to new ERP and Microsoft 365

In North Indianapolis today to set a couple Lenovo computers for a client.

Finishing up a server and firewall upgrade project near downtown Indianapolis.

Working in North Indianapolis this afternoon to setup a Lenovo Computer for a client.

Working in Carmel today to help a client with their network troubleshooting.

North side of Carmel working with a healthcare client on a Microsoft 365 consulting project

Working in Indianapolis today to assist a customer with IT support.

Working near downtown Fishers today. IT consulting visit with new logistics client.

In Columbus today helping a client with their network troubleshooting.

Downtown Indianapolis IT support for a medical client needing help with HIPAA.

Meeting a potential downtown Indianapolis client to assist them with their IT support and review the Microsoft 365 environment. Always fun to take to potential clients!

Starting off the day in Carmel, just north of Indianapolis, Indiana. Performed IT support tasks and new firewall installation.

In Zionsville this morning to assist a customer with IT support.

Finishing up onsite server to Microsoft Azure migration. Another downtown Indianapolis IT consulting project is complete.

Working in North Indianapolis today assisting customers with IT Support.

In Indianapolis today assisting customers with Network troubleshooting.
Thank you Leap team! Great work as always
8520 Allison Pointe Blvd, Suite 128,
Indianapolis, IN 46250